Major firmware updates begin May 15, 2025. Learn how to migrate Teams phones, rooms, and panels from Android Device Administrator to AOSP with best practices for Intune compliance and Conditional Access.
This is a follow up to our earlier article about the major upgrades to native Teams phones which began in 2024:
- The operating system on the phones will be upgraded to Android 12.
- Management of Native Teams phones in Intune will switch to the Android Open Source Project (AOSP) from the Android Device Administrator.
🚨 Quick Recap
See quick recap
Key Timeline Alert
- Auto updates begin:
- AudioCodes: May 15, 2025
- Poly: May 31, 2025
- Yealink: April 2025 (manual only, auto TBD)
What’s Changing?
Microsoft is shifting Teams Android devices from Android Device Administrator (ADA) to Android Open Source Project (AOSP) management via Intune. This shift affects:
- Teams Phones
- Teams Rooms
- Teams Panels
ADA End-of-Life:
Intune support for ADA ended December 31, 2024. Auto updates to AOSP firmware begin May 15, 2025. You must configure Intune with AOSP profiles before this date to avoid losing device management functionality.
What You Need To Do Now
1. Create AOSP Enrollment Profile
- Use “Corporate-owned, user-associated devices” under AOSP in Intune.
- Set Wi-Fi to “Not configured”
- Enable for Microsoft Teams devices
2. Configure AOSP Management Policy
- Platform: Android (AOSP)
- Profile Type: Device Restrictions
- Policy: Block Screen Capture = Yes
3. Create Compliance Policies (Per Device Type)
- Set separate policies for:
- Teams Phones
- Teams Rooms
- Teams Panels
- Use Intune filters and dynamic groups
- Ensure inclusion AND exclusion is properly scoped
4. Set Conditional Access Policies
- Separate policies for each device type
- Use filters/dynamic groups
- Exclude AOSP Teams devices from other org-wide CA and App Protection policies
5. No MFA on Meeting Room Accounts
- Resource accounts should be excluded from interactive MFA
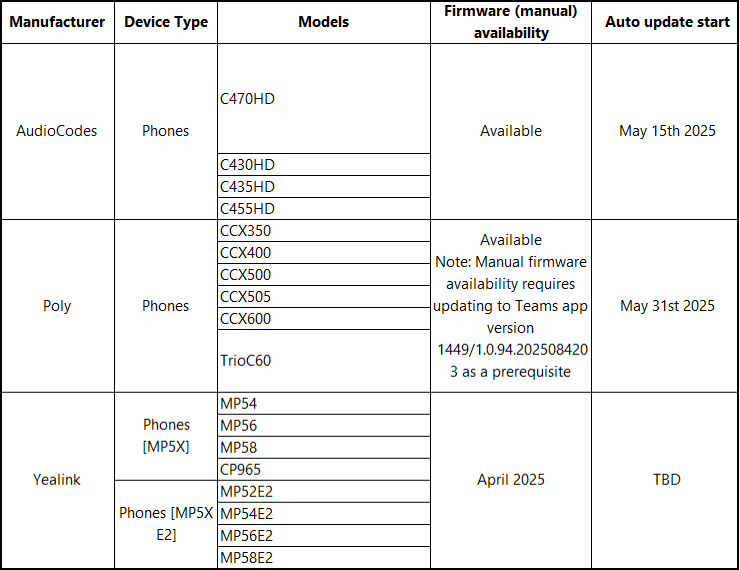
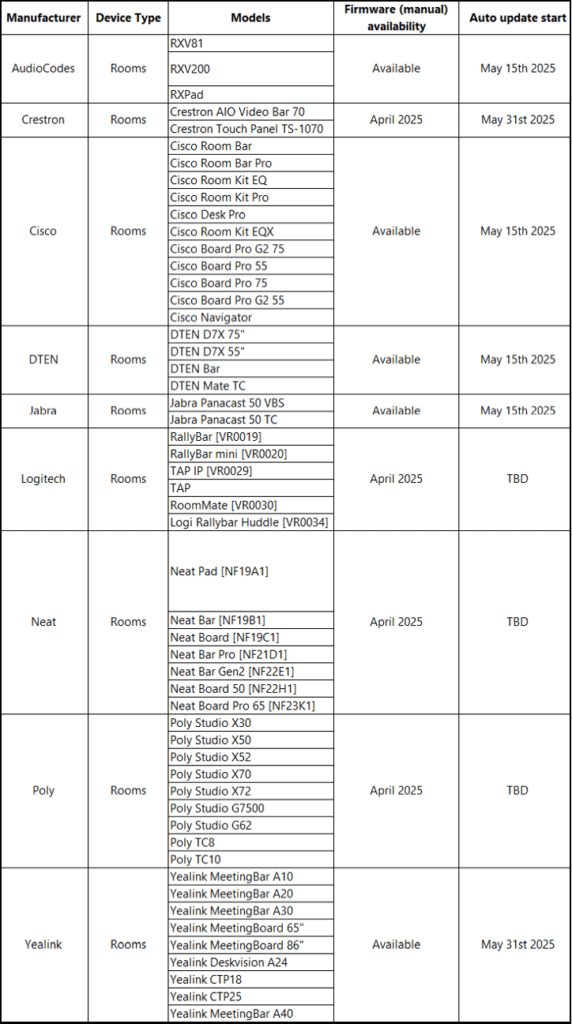
Firmware Update Details
| Manufacturer | Models | Manual Firmware | Auto Update Start |
|---|---|---|---|
| AudioCodes | C470HD, C435HD, CCX500, etc. | Available | May 15, 2025 |
| Poly | CCX Series, Trio C60 | Available (1449/1.0.4920508240.3 required) | May 31, 2025 |
| Yealink | MP54, MP56, MP58 | April 2025 | TBD |
Full details available at:
Moving Teams Android Devices to AOSP – Microsoft Community Hub
Best Practices Summary
- Use Microsoft’s best practice on authentication and conditional access
- Exclude all Teams devices from default compliance and CA policies
- Use Intune Filters by model/manufacturer
- Segment Policies: Avoid bundling Teams phones, rooms, and panels into one policy
- Don’t Delay: Do all AOSP preparation before May 15, 2025
Latest News
- The firmware updates to add support for AOSP management under Intune will begin to be applied by auto updates in the Teams Admin Center (TAC) starting on May 15, 2025.
- These updates will be available for these Teams Android phones, rooms, and panels.
- The updates cannot be paused and will be applied based on the update phase (Validation, General, and Final) assigned to the device. Review these links for more on device update phases:
- For rooms and panels: Update Microsoft Teams devices remotely – Microsoft Teams | Microsoft Learn
- The update schedule was provided in Moving Teams Android Devices to AOSP Device Management | Microsoft Community Hub
Teams Android Phone Updates
See Teams Android Phone Updates
Teams Android Room Updates
See Teams Android Room Updates
Teams Android Panel Updates
See Teams Android Panel Updates
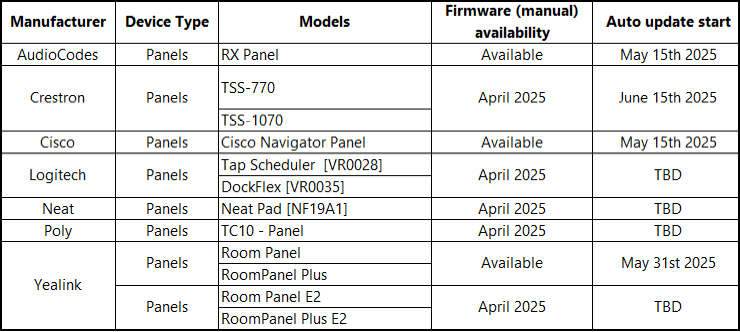
Teams Android Display Updates
See Teams Android Display Updates
Microsoft has published Migrating Teams Android Devices to AOSP Device Management from Device Administrator. This article describes:
- How to configure Intune to enroll and manage Native Teams phones that use the AOSP management platform.
- Some organizations have added enrollment, compliance, and conditional access policies to Intune to manage native Teams phones. This article tells you what to do to prepare to move these managed phones from the Android Device Administrator platform to the AOSP platform. This must be set up before installing the AOSP-supported software on your devices.
Intune & Teams Devices: What You Need to Know
Two (2) years ago, I summarized the information from Microsoft about how to enroll native Teams phones in Intune managed through Android Device Administrator (ADA):
Native Teams phones, rooms, and panels running the Android 9 operating system have been running under Android Device Administrator (ADA) platform for many years. Intune ended support for ADA beginning December 31, 2024.
- If you’ve enrolled native Teams phones, rooms, or panels in Intune using the Android Device Administrator (ADA) platform, you should have already prepared for the end of support.
- Complete all required steps before installing the AOSP software upgrade on any enrolled Teams device. Deadline: May 15, 2025
- If you’ve implemented the AOSP enrollment policy in Intune, Microsoft confirms that:
- When a native Teams phone, room, or panel is upgraded,
- Intune will automatically re-enroll the device using AOSP enrollment.
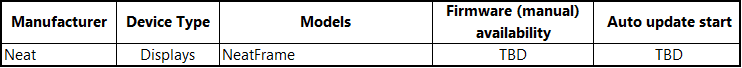
We created the AOSP enrollment policy in our tenant during the fall of 2024. In January, the AOSP update for the AudioCodes phones became available, and on March 5, 2025, the update for (at least) one of our Poly CCXs appeared in the Teams Admin Center.
Intune Enrollment prior to applying the AOSP Update:
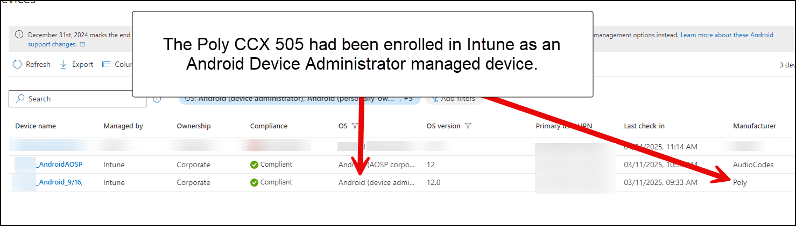
Intune Enrollment after updating the device to support AOSP:
Intune Configuration
The steps to set up AOSP-managed native Teams phones are similar to those in the original articles. Rather than completely reproduce those blogs here, I will just describe what has changed. I have also included guidance for creating the policies for Teams Rooms and Teams Panels, which I had not previously covered.
❗ IMPORTANT NOTE
Microsoft in the article Conditional Access and compliance best practices for Microsoft Teams Rooms – Microsoft Teams | Microsoft Learn under the “Teams Rooms Conditional Access best practices” section recommends that you “Exclude your Teams Rooms resource accounts from all existing Conditional Access policies and create a new policy specific to the resource accounts.” This guidance also applies to the Teams phones and panels. To elaborate and clarify this point:
- Create Intune filters, as described in the earlier blogs, for your Android Teams phones, Teams rooms and panels.
- Here is an example filter for several models of AudioCodes and Poly Android Teams rooms systems:((device.manufacturer -eq “AudioCodes”) and (device.model -in [“RXV200″,”RXPad”,”RXV81″])) (or (device.manufacturer -eq “Poly”) and (device.model -in [“X30″,”X50”]))
- Since you sign on to Teams room and panels using a Meeting Room resource account, use a naming standard for these accounts. This will make it easier to use dynamic groups in Microsoft Entra to automatically apply Compliance and Conditional Access policies to these devices. It will also make it easier to exclude these from all other Compliance and Conditional Access policies (see below).
- Create separate policies for your phones, rooms and panels. You may thank me for this in the future! Include the phones, rooms and panels on these policies using a combination of the Intune filter and/or dynamic groups.
- Use the filters and/or dynamic groups as inclusion criteria on the Compliance and Conditional Access policies created for the phones, rooms and panels.
- Exclude the phones, rooms and panels from all other Compliance and Conditional Access policies. Again, you can use the filter and/or dynamic groups to apply the exclusions.
- Guidance for this can be found in the 2nd article. Search for “Add the Teams Phones Exclusion Query as a “Filter for Devices” Condition on Existing Conditional Access Policies including Terms of Use Policies that have Unsupported Teams Phones Settings.”
- Do not require interactive multifactor authentication (MFA) for your Meeting Room resource accounts.
- Consult these articles regarding authentication best practices for Teams phones, rooms and panels (this subject will be covered in a future article):
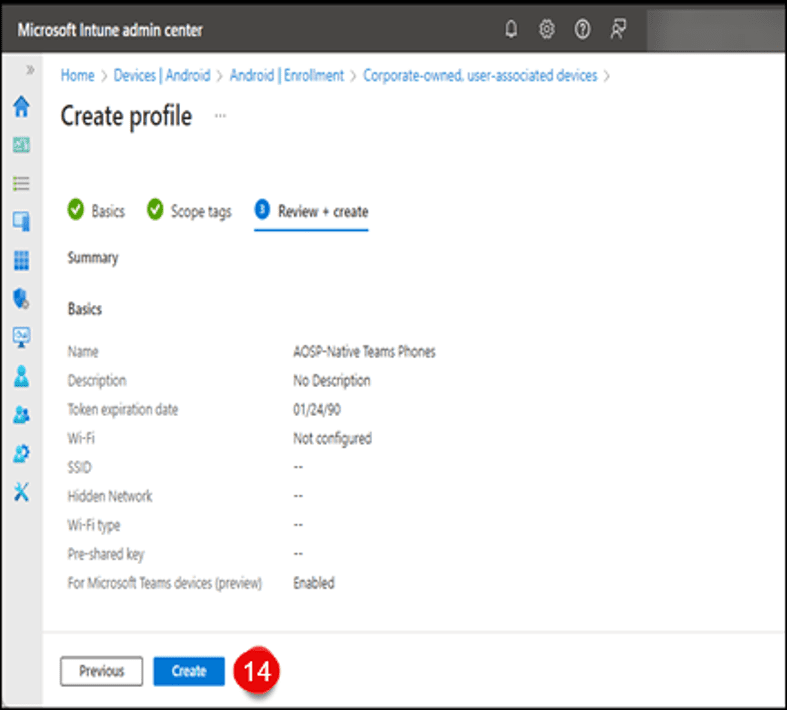
Adding AOSP Enrollment Profile
- Sign into the “Microsoft Intune admin center.”
- Click on “Devices.”
- Click on “Enrollment.”
- Under “Android Open Source Project (AOSP),” click “Corporate-owned, user -associated devices.”
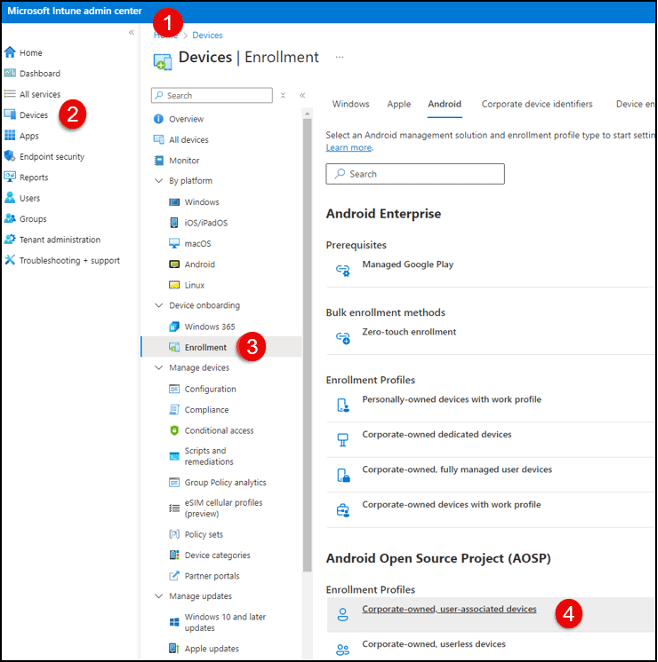
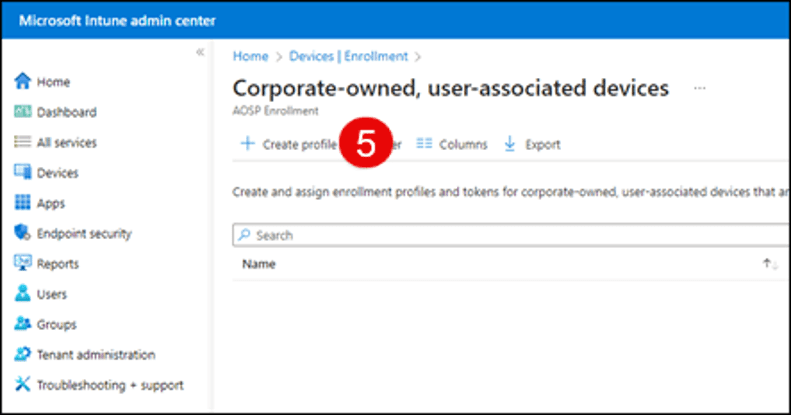
- Click “Create profile.”
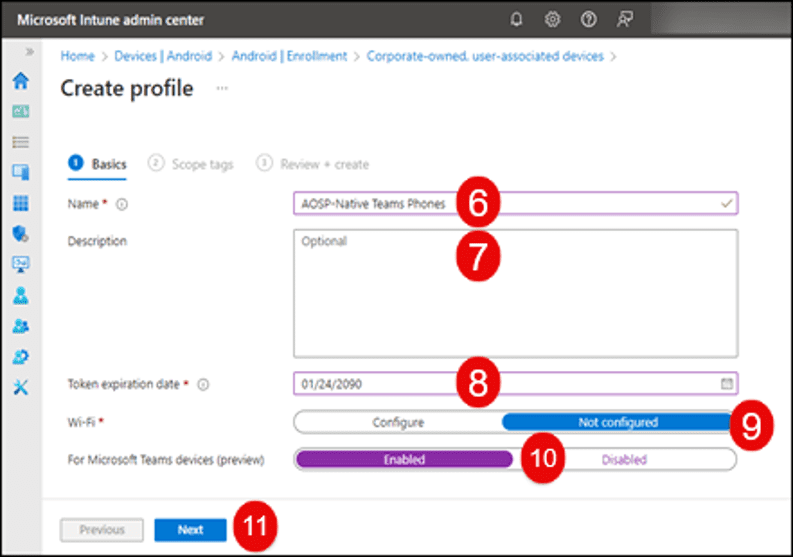
- Type in a name for the profile.
- Optionally, add a description.
- An expiration date sixty-five (65) years in the future will be provided. Leave this default expiration date as is.
- Set “Wi-Fi” to “Not configured.”
- Select “Enabled” for “For Microsoft Teams devices.”
- Click the “Next” button.
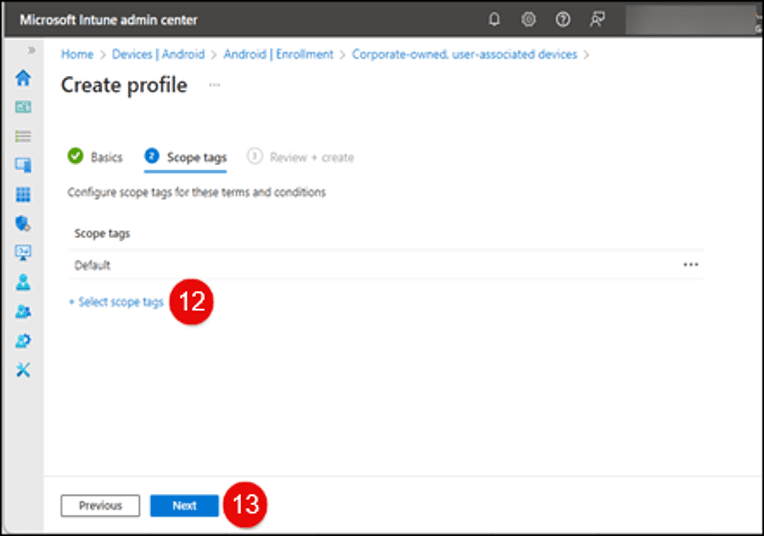
- Select “Scope Tags” as needed.
- Click the “Next” button.
- Click the “Create” button on the next screen.
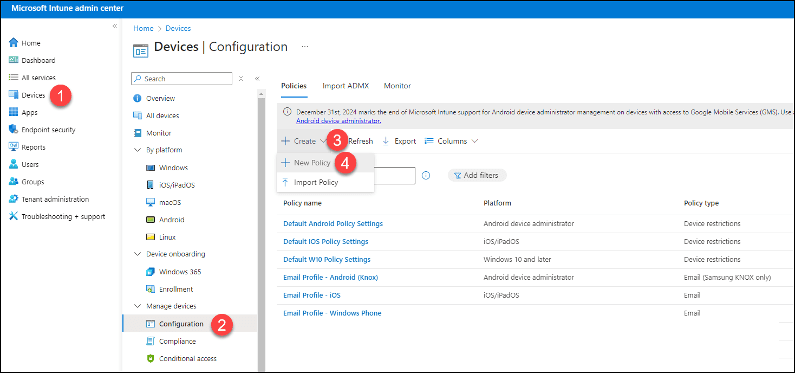
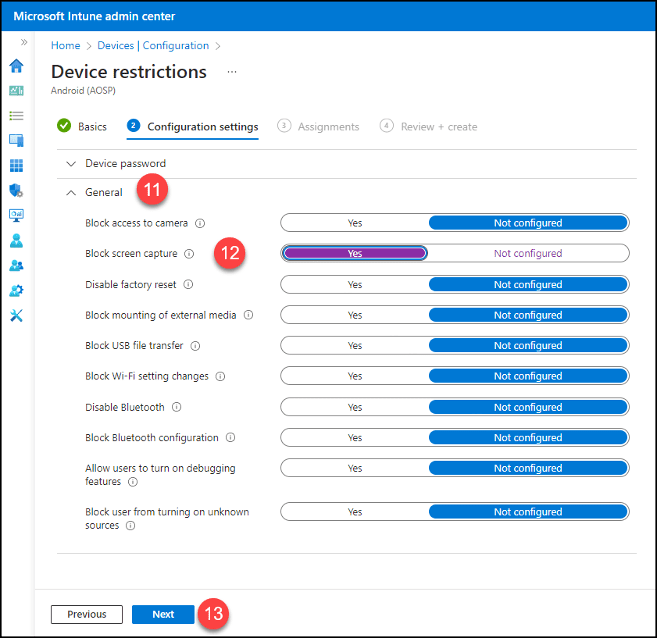
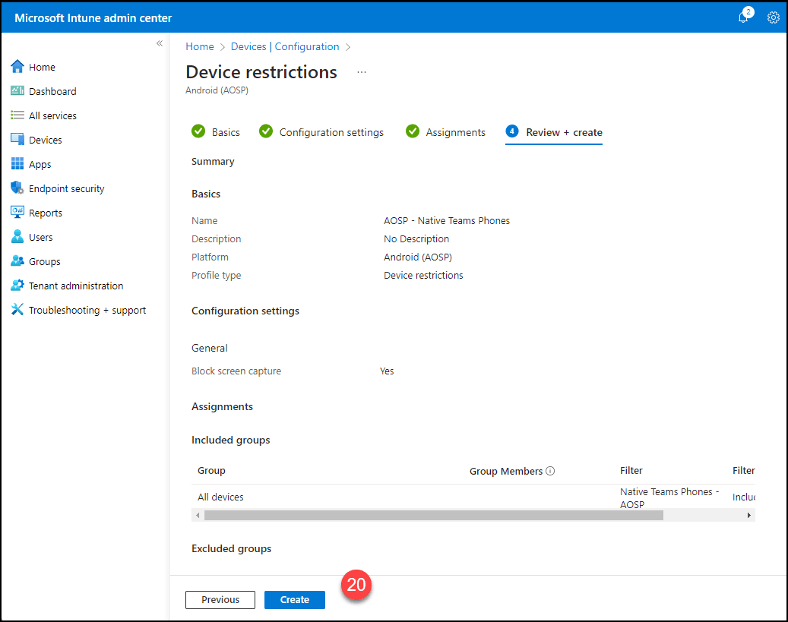
Creating an AOSP Management Configuration Policy
- Click on “Devices.”
- Click “Configuration.”
- Under the “Policies” tab, click the “Create” drop-down menu.
- Click “New Policy.”
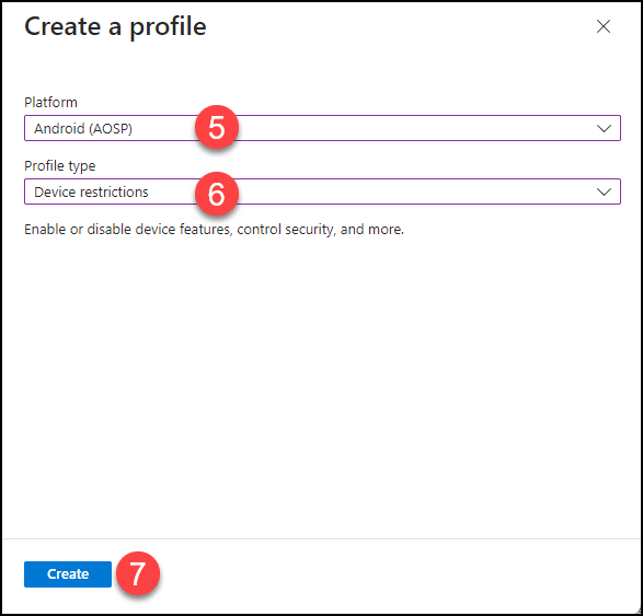
- In the “Create Profile” window, select “Android (AOSP)” from the “Platform” drop-down menu.
- From the “Profile type” drop-down menu, select “Device restrictions.”
- Click the “Create” button.
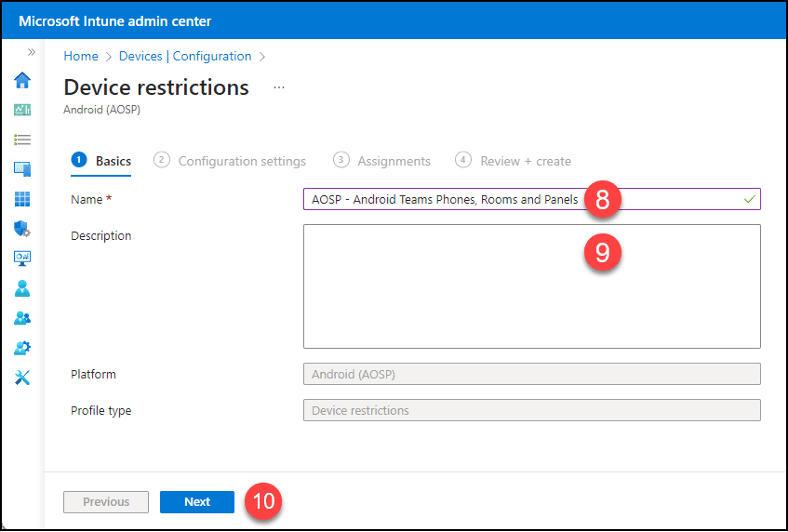
- Provide a name for the policy.
- Optionally, add a description.
- Click the “Next” button.
- Click on “General.”
- Click “Yes” for “Block Screen Capture.” This is the only setting that Microsoft supports for Teams phones, rooms and panels currently.
- Click the “Next” button.
- Click the “+ Add all devices” button.
- Click “Edit filter.”
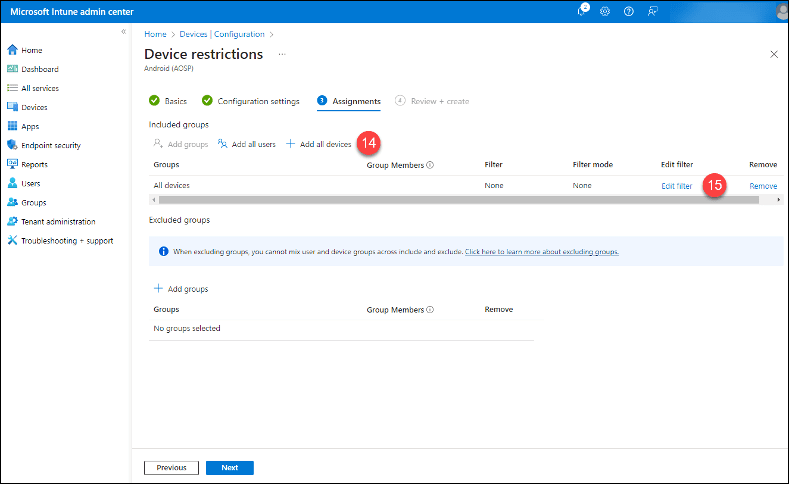
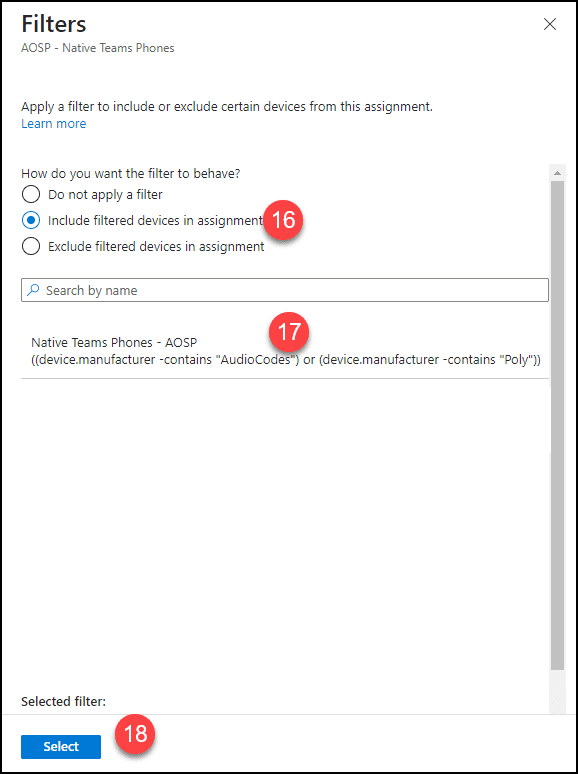
- Click on the “Include filtered devices in assignment” button.
- Click on the appropriate filter for native Teams phones.
- Click the “Select” button.
- Click the “Next” button.
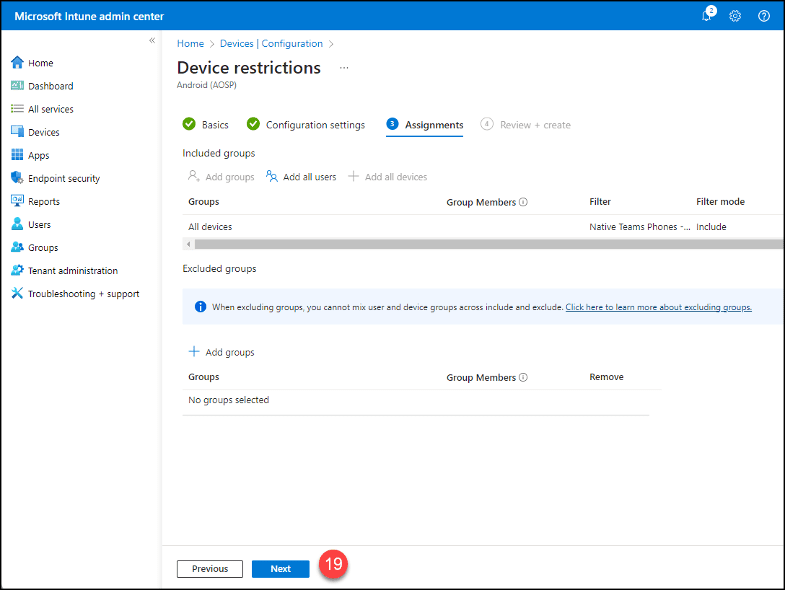
- Click the “Create” button.
Creating a Device Compliance Policy for Teams Phones
- Follow the steps in the first blog article. At step “3”, choose “Android (AOSP)” instead of “Android Device Administrator”.
- Provide a new unique name for the policy and add a description as needed.
- The Intune Compliance Policy Options for the Teams phones from September 14, 2022, remain the same.
- Use the previously created Teams Phones Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
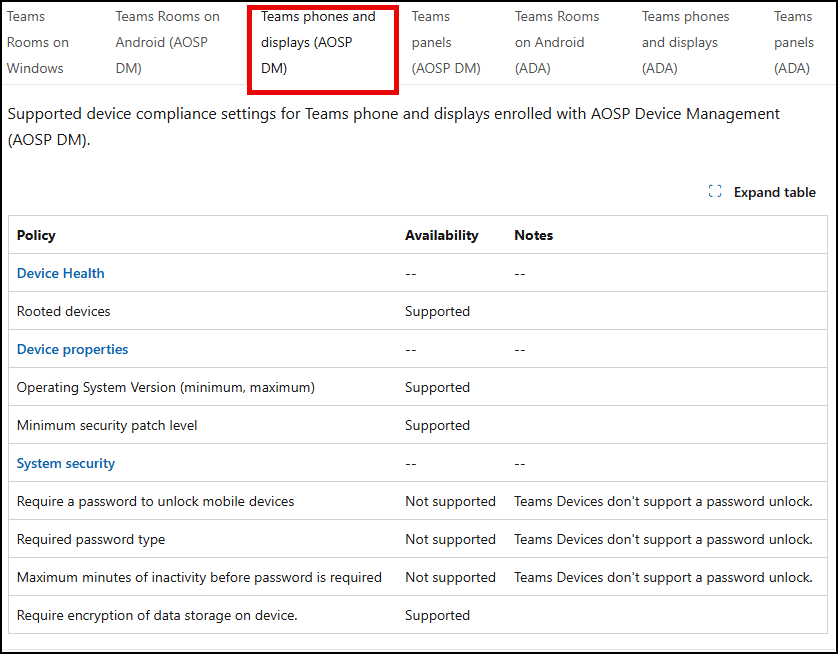
Creating a Device Compliance Policy for Android-Based Teams Rooms
- Follow the steps in the first blog article. At step “3”, choose “Android (AOSP)” instead of “Android Device Administrator”.
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Rooms Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
- The supported Compliance Policy settings for Teams rooms and panels are the same. They can be found at Supported Conditional Access and Intune device compliance policies for Microsoft Teams Rooms – Microsoft Teams | Microsoft Learn and in the following table (Note: “Device managed with device administrator” in the “Device Health” section of the properties is not available in Intune):
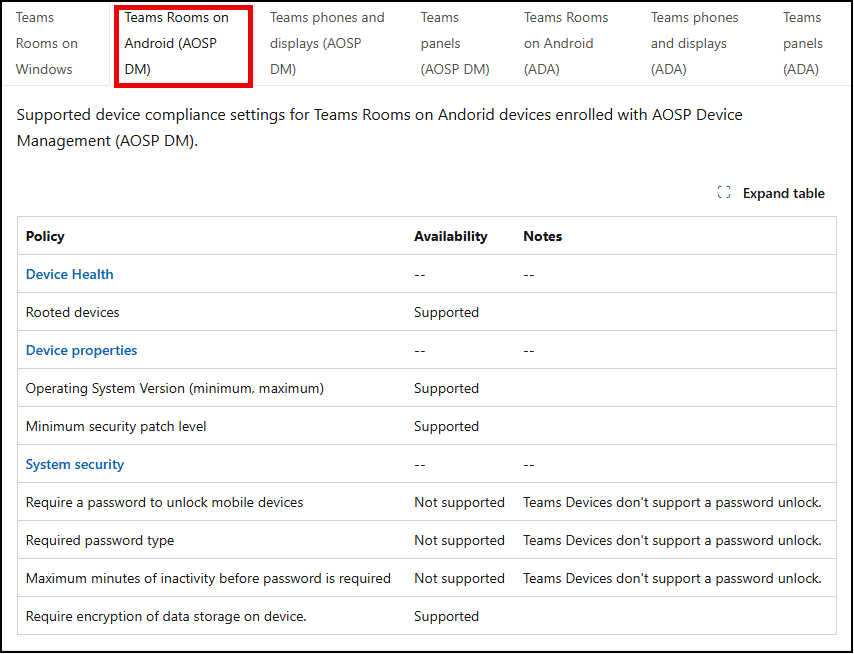
Creating a Device Compliance Policy for Android-Based Teams Panels
- Follow the steps in the first blog article. At step “3”, choose “Android (AOSP)” instead of “Android Device Administrator”.
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Panels Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
- The supported Compliance Policy settings for Teams rooms and panels are the same and are listed above.
Creating a Conditional Access Policy for Teams Phones and Displays
- Follow the steps in the second blog article at the “Create a Teams Phones Conditional Access Policy.”
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Phones Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
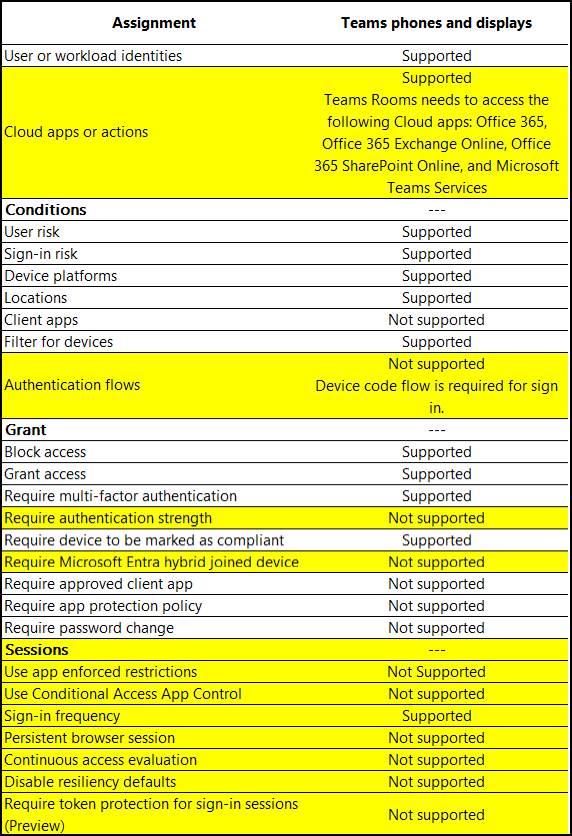
- There have been some changes to the supported elements in the Conditional Access Policies for Teams phones from the earlier articles. The differences have been highlighted in the following table:
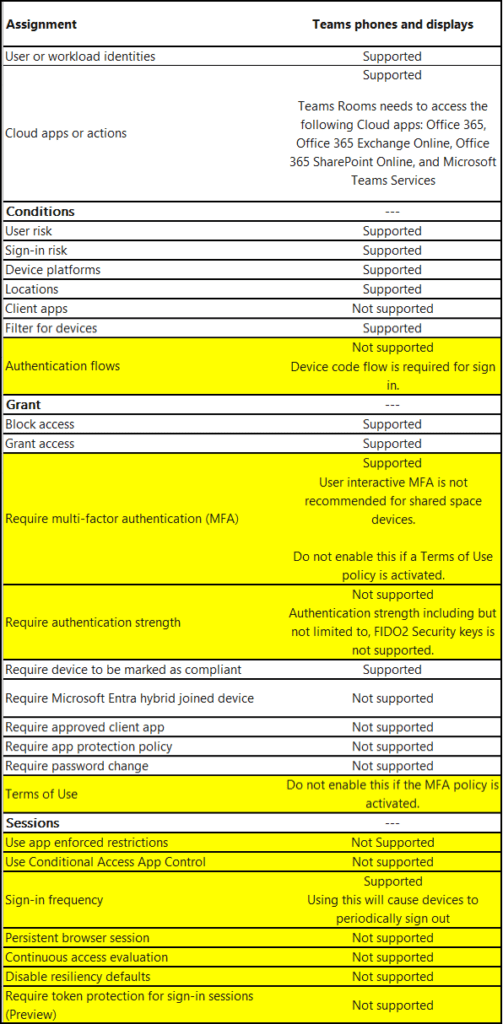
Creating a Conditional Access Policy for Teams Phones
- Follow the steps in the second blog article at the “Create a Teams Phones Conditional Access Policy.”
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Phones Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
- There have been some changes to the supported elements in the Conditional Access Policies for Teams phones from the earlier articles. The differences have been highlighted in the following table:
Creating a Conditional Access Policy for Teams Rooms
- Follow the steps in the second blog article at the “Create a Teams Phones Conditional Access Policy.”
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Rooms Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
- The Conditional Access Policy element support for the rooms and panels are identical:
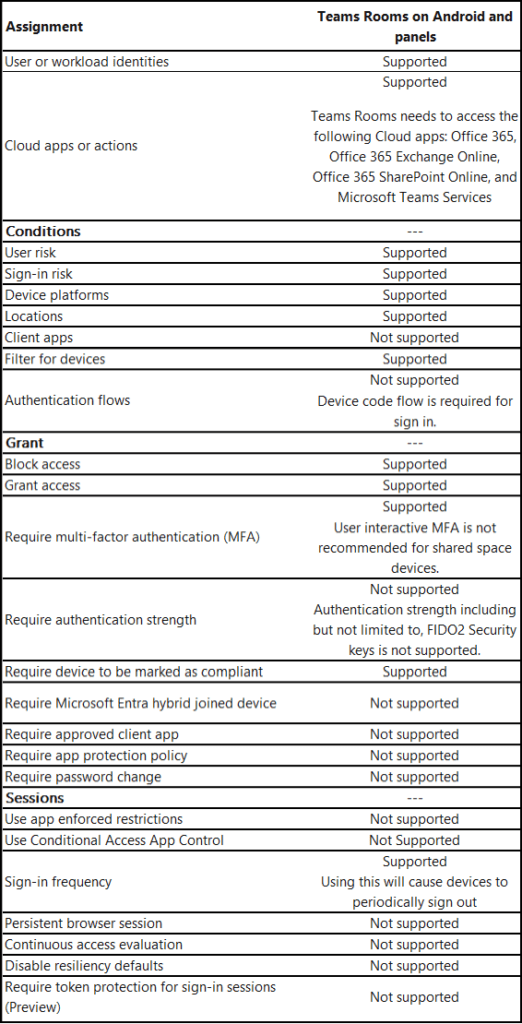
Creating a Conditional Access Policy for Teams Panels
- Follow the steps in the second blog article at the “Create a Teams Phones Conditional Access Policy.”
- Provide a new unique name for the policy and add a description as needed.
- Use the previously created Teams Rooms Intune filter as the inclusion criteria when applying the “All Devices” group to the policy.
- The Conditional Access Policy element support for the rooms and panels are identical. Refer to the previous table.
Excluding Android Open System Project devices from App Protection Policies
- If you had created this based on the two (2) older blogs, you should be good to go. You can check it to verify that “Android (AOSP) user associated devices” and “Android (AOSP) userless devices” are listed under the device types of the policy.
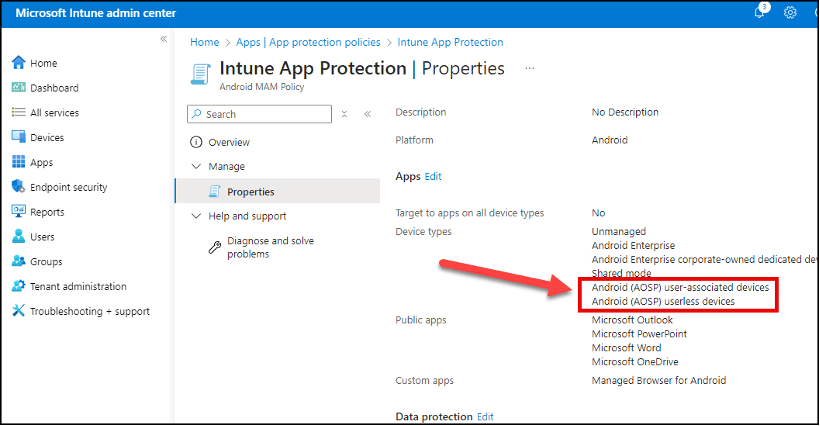
- If you have not created this policy, follow the guidance in the older articles.
Final Thoughts
Microsoft is getting “serious” about upgrading Teams Android phones, rooms, and panels to include support for AOSP.
Microsoft was originally set to deprecate Android Device Administrator (ADA) from Intune on December 31, 2024, but the platform is still active. Now, a more definitive sunset date is on the horizon.
Organizations that use Intune to manage devices signed into with Teams accounts should take heed:
You must ensure Intune is properly configured to support devices running AOSP.
While Microsoft has not provided specifics, it should be inferred that Teams devices currently managed via ADA will cease to be managed once ADA is officially retired in Intune.
If your organization requires enrollments for all devices, and ADA management suddenly stops working, you’re going to have a problem.

How eGroup Can Help
If you’re unsure how to migrate Teams phones, rooms, and panels from Android Device Administrator to AOSP, or need help with best practices for Intune compliance and Conditional Access, we’ve got your back.
Get AOSP-Ready Before May 15
Avoid downtime and losing control over your devices. Let our experts help you implement AOSP enrollment, filters, and conditional access with zero disruption.